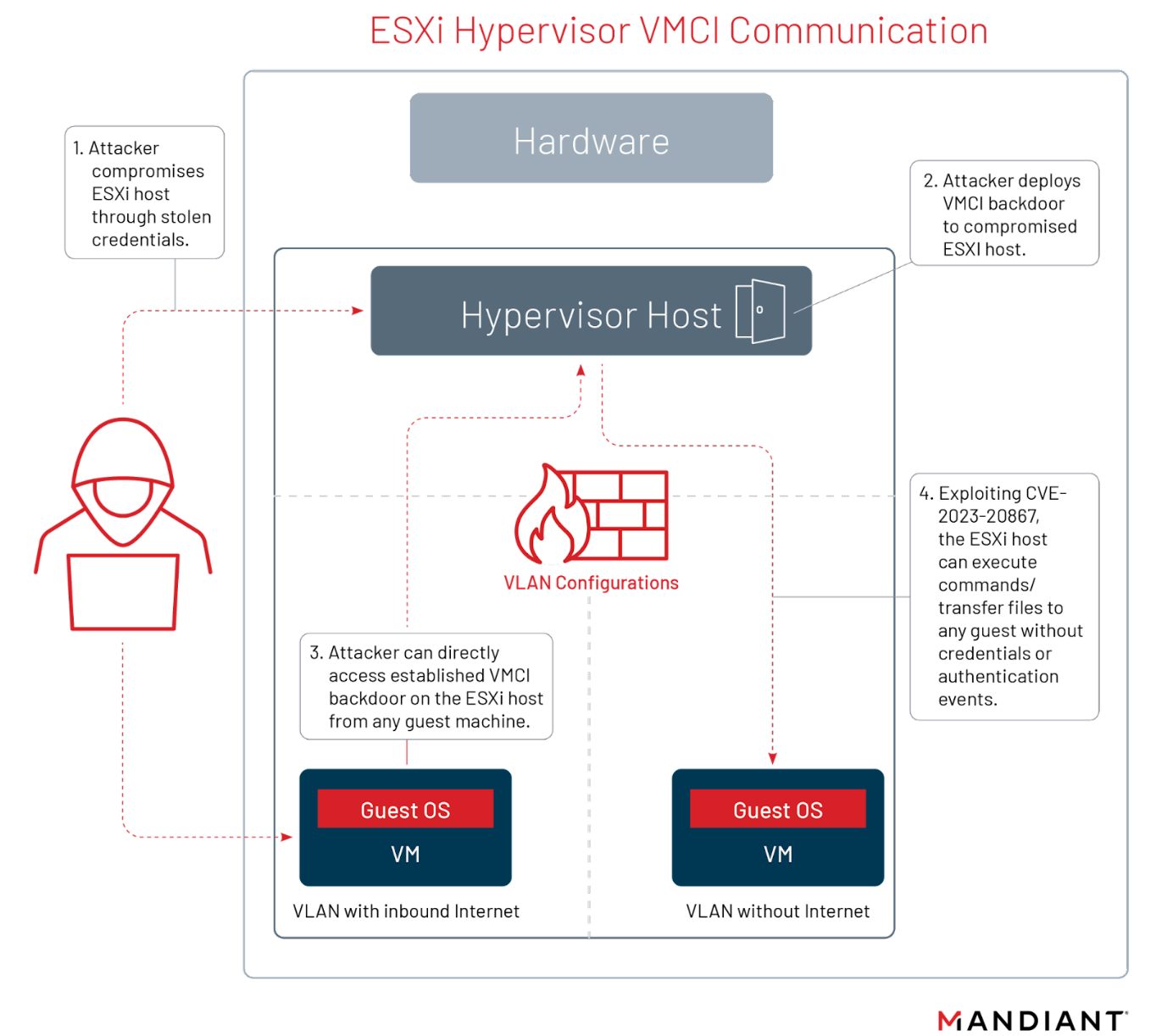
Detection, Containment, and Hardening Opportunities for Privileged Guest Operations, Anomalous Behavior, and VMCI Backdoors on Compromised VMware Hosts | Mandiant
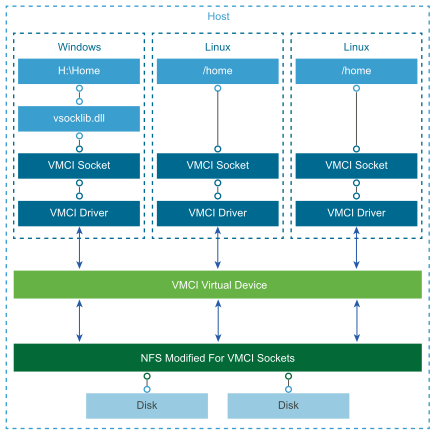
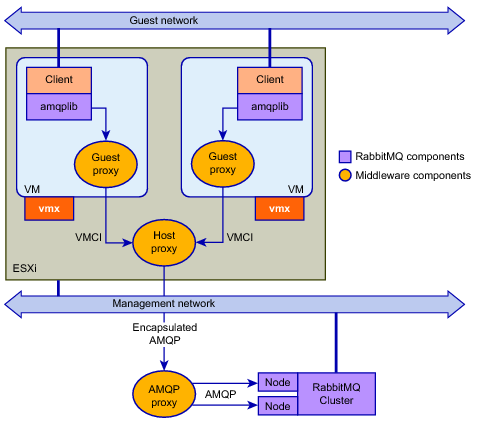
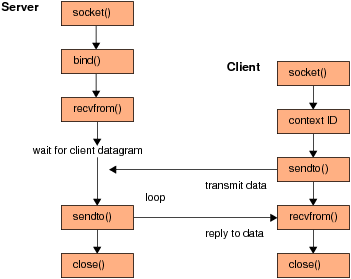
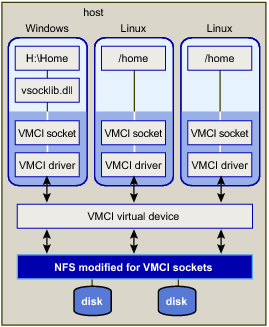
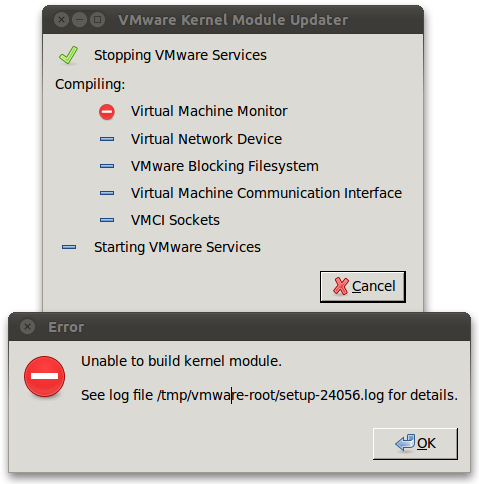
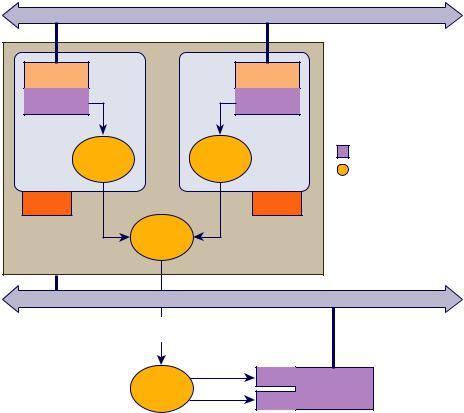
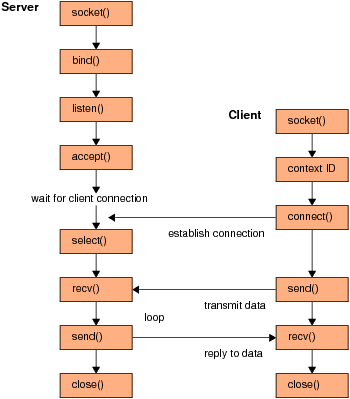
GitHub - scottt/python-vmci: Python's socket patched with VMCI (VMware communication interface) support
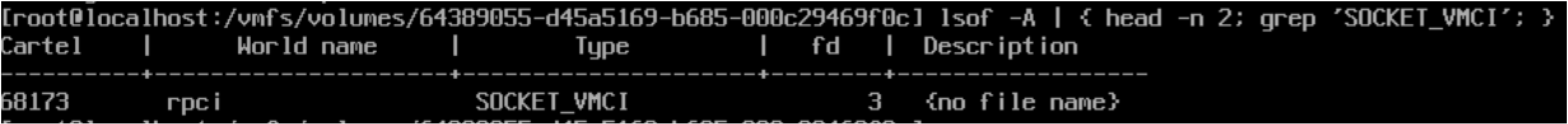
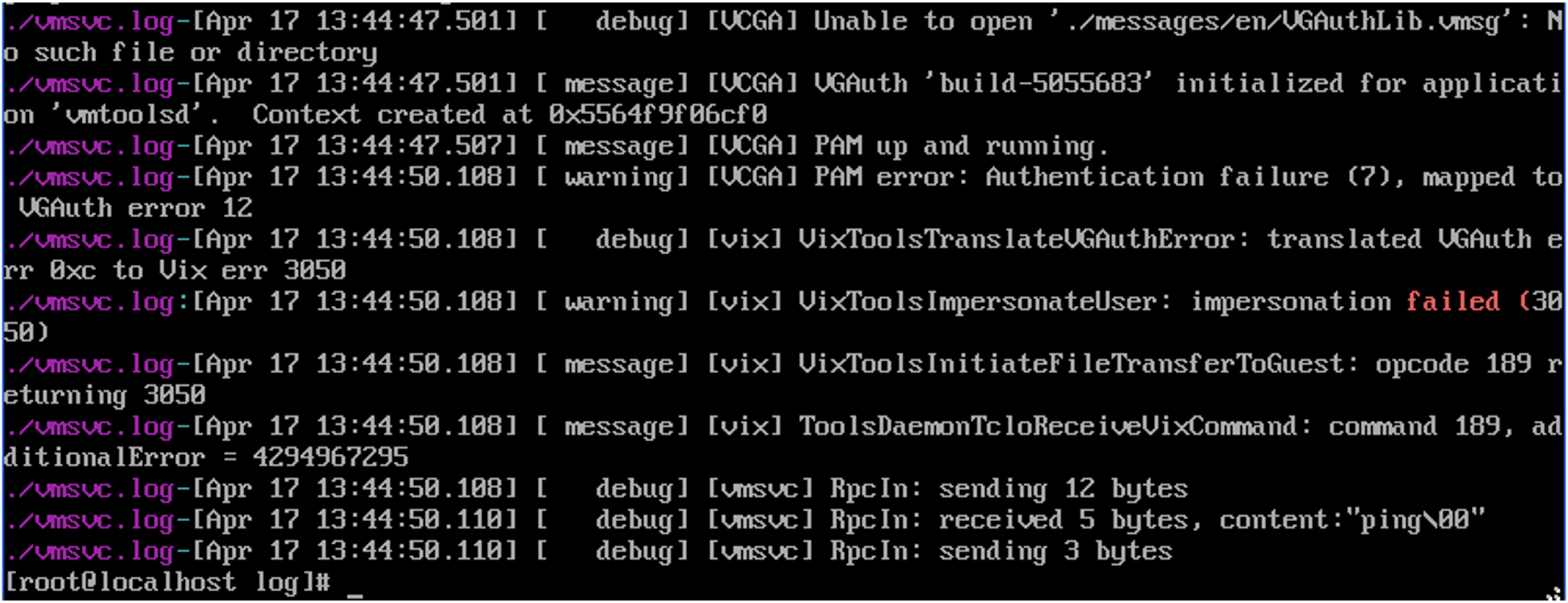
Detection, Containment, and Hardening Opportunities for Privileged Guest Operations, Anomalous Behavior, and VMCI Backdoors on Compromised VMware Hosts | Mandiant
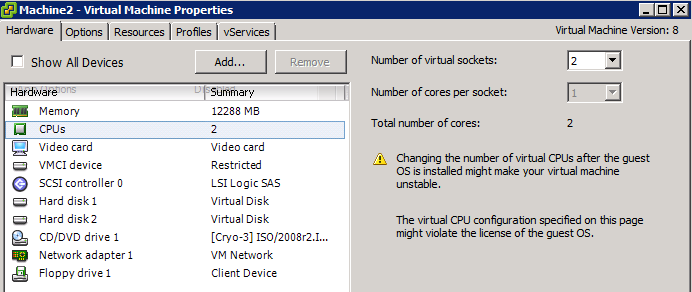
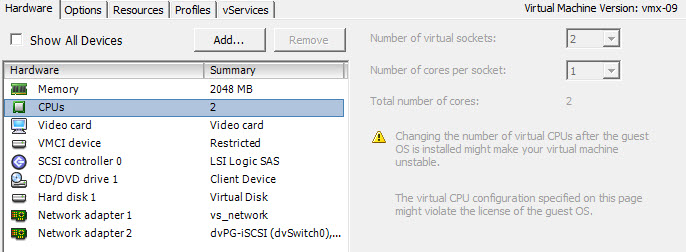
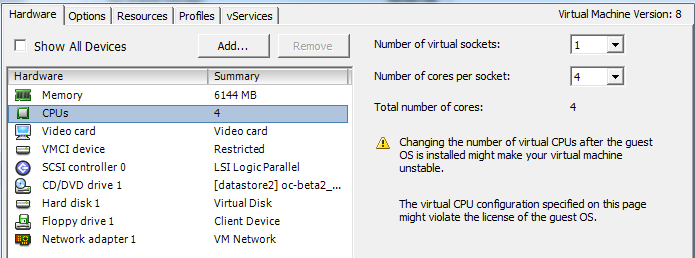
vCPU configuration. Performance impact between virtual sockets and virtual cores? - frankdenneman.nl